EXPLORE. LEARN. HACK.
Hands-on cybersecurity courses to take you from rookie to unstoppable.
 BASICS
BASICSFundamentals
Start here. In this course, we go through important basics that enable in-depth learning of increasingly complex topics in information security. The course is intended for students who are new to information technology.
 WEB
WEBBurpSuite - Fundamentals
BurpSuite is the leading web application security tool that facilitates identification and exploitation of vulnerabilities in web applications using various tools.
 CODE
CODEPython Programming
Let's learn the basics of programming with Python. Aimed at complete beginners.
 CODE
CODEJavaScript
Learn programming with JavaScript, arguably the most important and versatile programming language in today's world, at least for web development.
 CODE
CODEBasics of web development
This course is an introduction to web development and focuses on the basics of HTML, CSS, JavaScript and backend systems. The aim of the course is to provide students with the necessary skills and knowledge to design, develop and understand simple web applications.
 WEB
WEBSQL Injection
SQL injection is probably the cause of the majority of serious data breaches, mainly because vulnerability is very likely in a large application if the technology choices are bad, and the result is usually leaking the entire database to the attacker.
 CRYPTO
CRYPTOPassword attacks
Passwords are terribly insecure for an awful lot of reasons, but still necessary. A dangerous combination!
 WEB
WEBCommand injections
One of the scariest places an injection vulnerability can hit is operating system commands. The penalty is almost always a complete takeover of the server by the attacker. However, these vulnerabilities are found quite often when the application uses, for example, command line tools behind the scenes.
 WEB
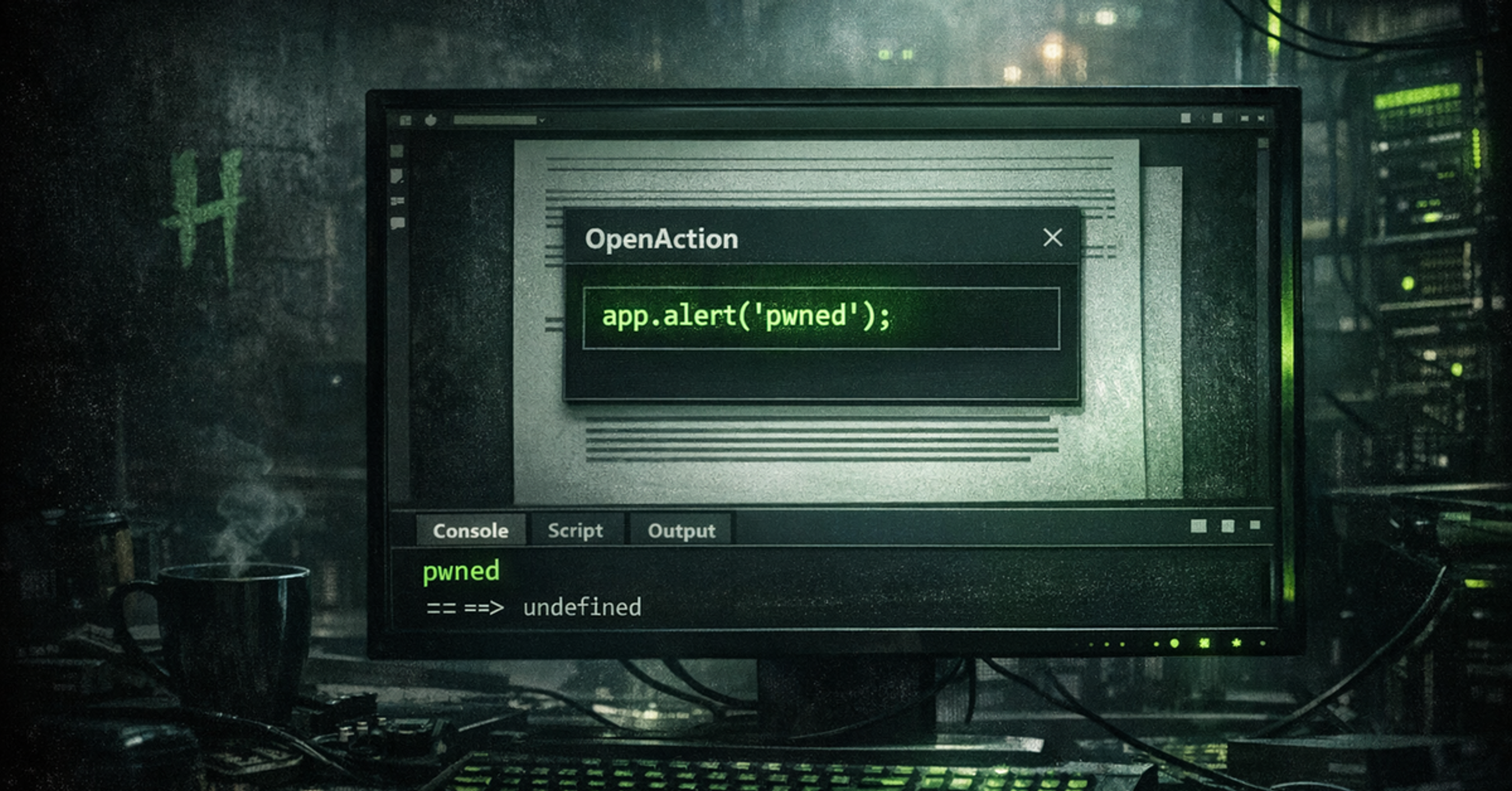
WEBXSS (Cross-Site Scripting)
Learn how to find and exploit a vulnerability that is one of the most common vulnerabilities, easy to find, and yet very dangerous. Hackerone ranked XSS the #1 bug bounty vulnerability of 2021.
 WEB
WEBJWT Attacks
There are JWT tokens almost everywhere you look these days. However, the choice or configuration of the JWT library often goes wrong, which can lead to token forgery, which in turn typically leads to a total breach of the application's security.
 WEB
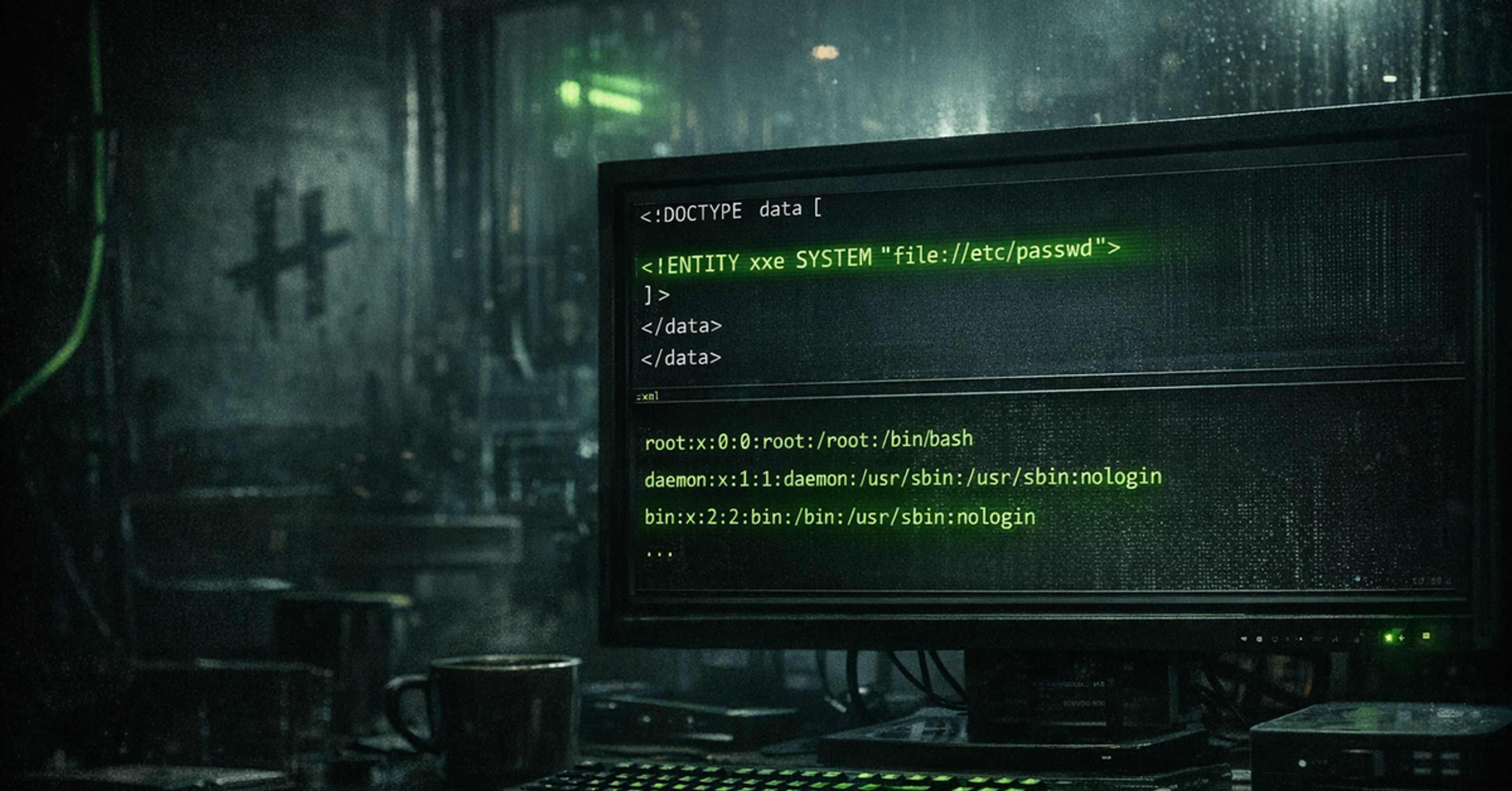
WEBXXE (XML External Entity) Attacks
XML is superficially a simple protocol, tags and attributes. However, XML has hidden capabilities that unfortunately are often not disabled by default in XML handlers...
 WEB
WEBLFI / RFI
A vulnerability that has historically plagued PHP applications in particular and can still be found in the wild, especially in old web applications.
 WEB
WEBAccess control vulnerabilities
Development is developing and thanks to modern application frameworks, traditional injection vulnerabilities or authentication problems are constantly being seen less and less. However, there is one thing that seems to always remain as difficult to implement safely, and that is the access control of a complex application.
 WEB
WEBURL injection
Injections can sometimes be found in surprising places, and building URLs is a common place where developers forget to consider the danger.
 WEB
WEBTemplate Injection Vulnerabilities
HTML is typically built with templates precisely to avoid injection vulnerabilities, but sometimes it happens so miserably that the injection hits the template itself, and in that case the consequences are serious.
 WEB
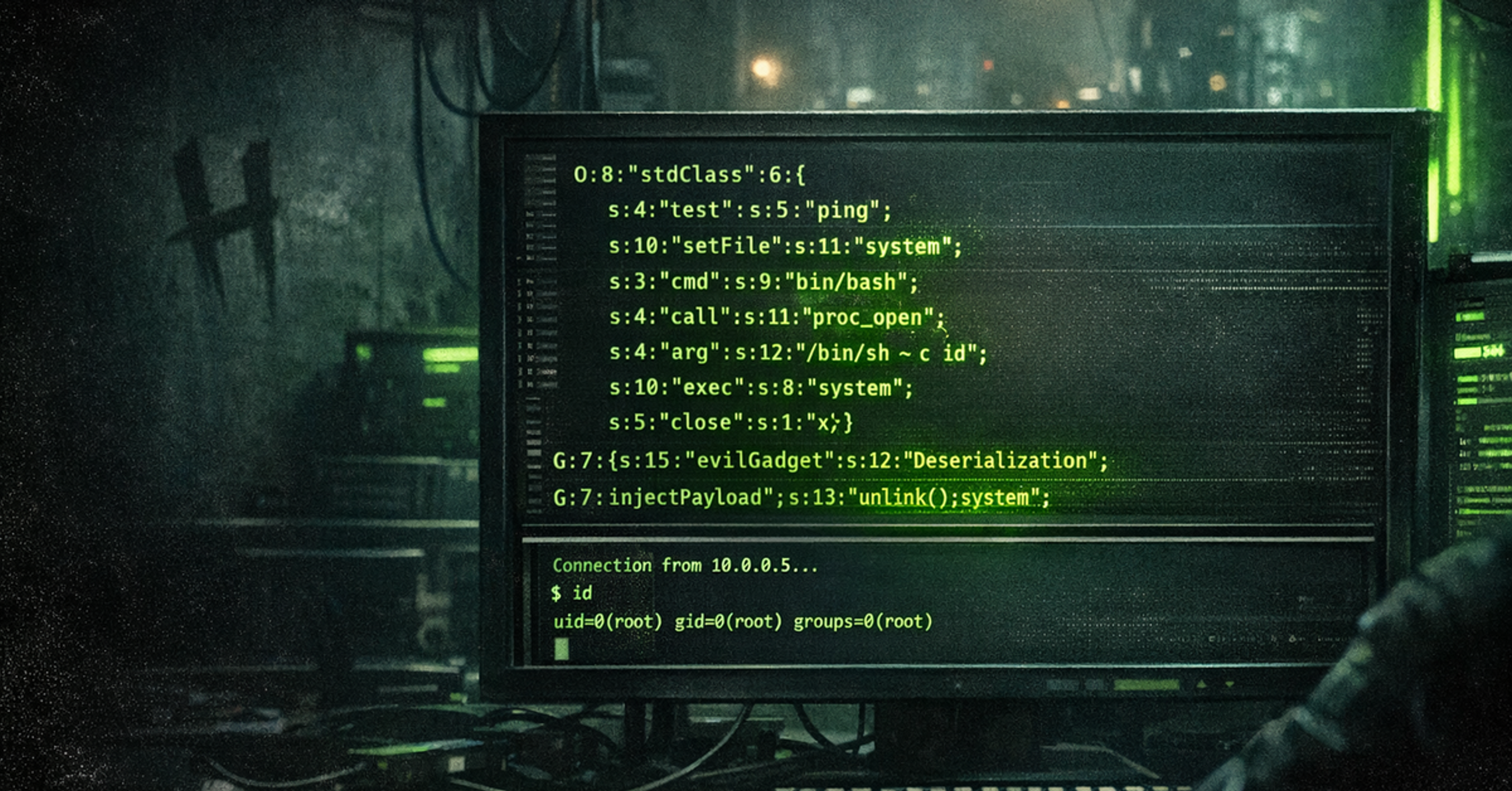
WEBDeserialization Attacks
Serialization is an extremely easy and convenient way to get complex states saved on disk or transferred over the network. However, ease brings with it a dark side, dismantling a serialized object can be compared to dismantling a bomb. It has to be done just right or the consequences can be catastrophic.
 OSINT
OSINTOSINT
In today's world, the value of information has reached an all-time high. But did you know that a vast amount of useful – even critical – information is available completely openly? This is called OSINT, or Open Source Intelligence – intelligence gathered from publicly accessible sources.
 WEB
WEBBrowser security
The browser is a versatile environment, with code from completely different parties running in different tabs and windows, and these web applications are still able to communicate with each other. Such an environment has its risks!
 SYSTEMS
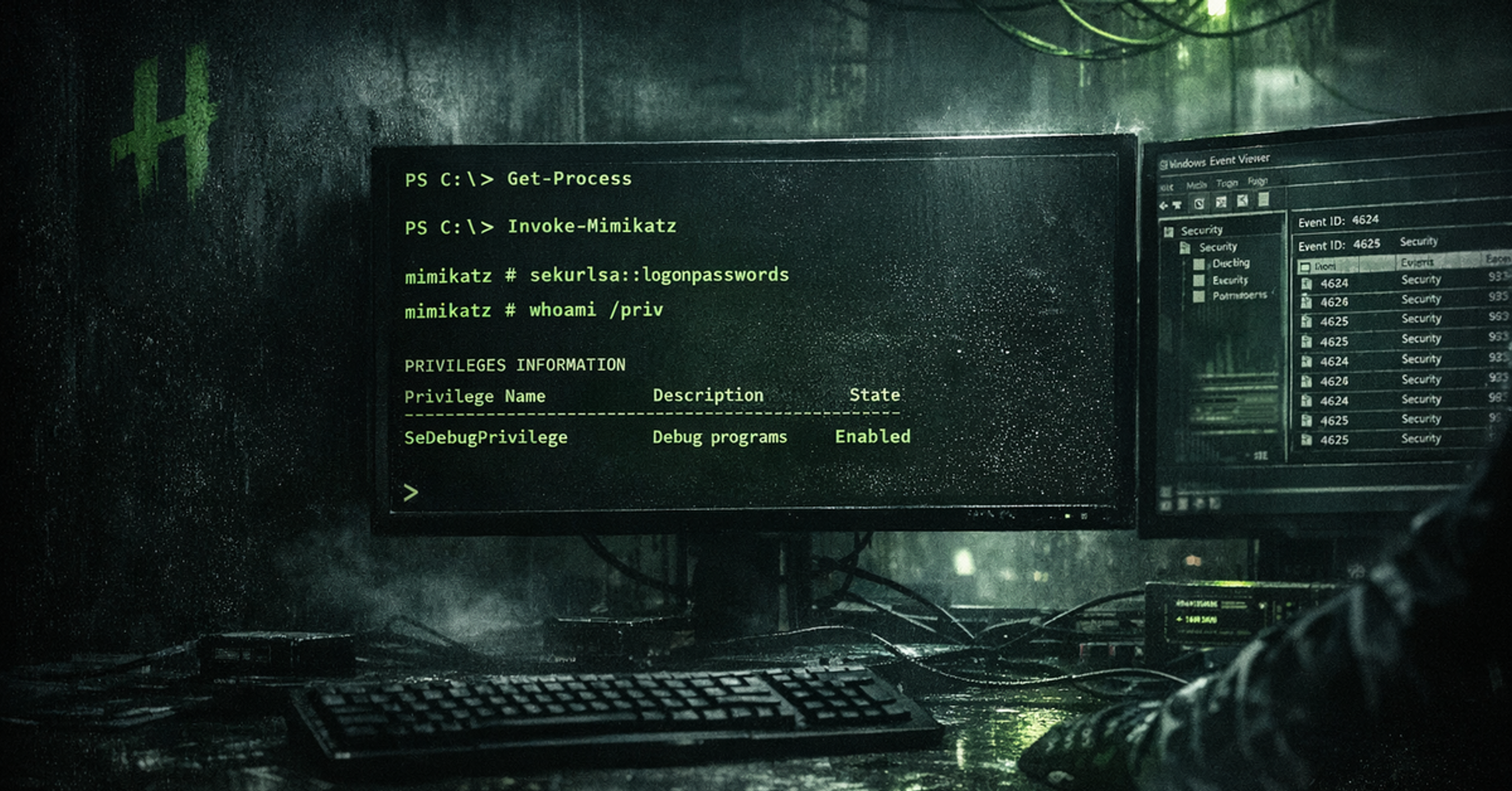
SYSTEMSWindows - Attack and Defense
Windows and Active Directory attacks and defense
 NETWORK
NETWORKNmap
Nmap is one of the most well-known tools that you can use to perform versatile network scans. Every information security professional should know how to use this tool.
 SYSTEMS
SYSTEMSWindows information security basics
In this course, we go through the basics related to managing Windows systems and maintaining information security.
 SYSTEMS
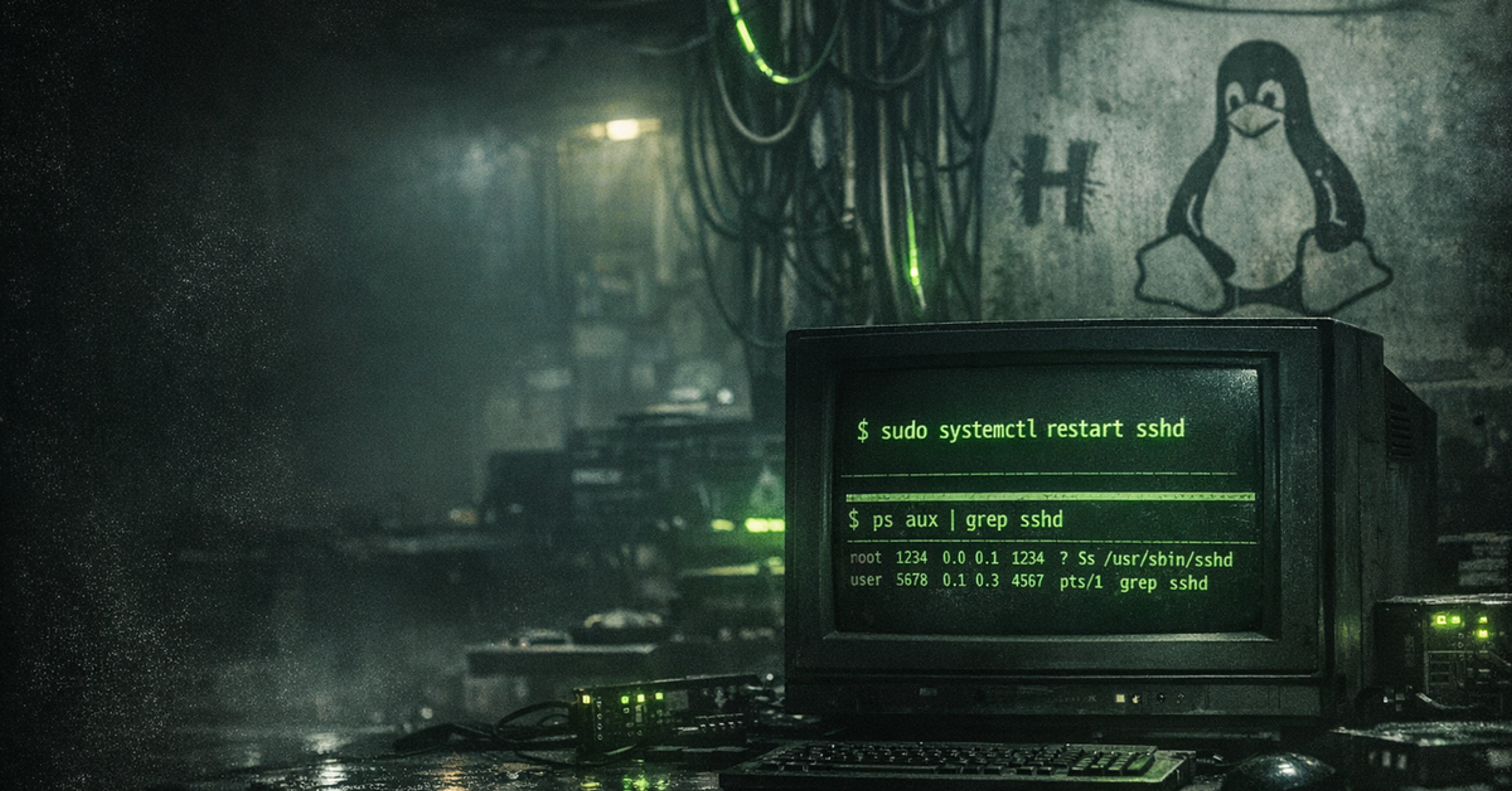
SYSTEMSLinux management and hardening
In this course, we go through topics related to managing and hardening Linux systems
 WEB
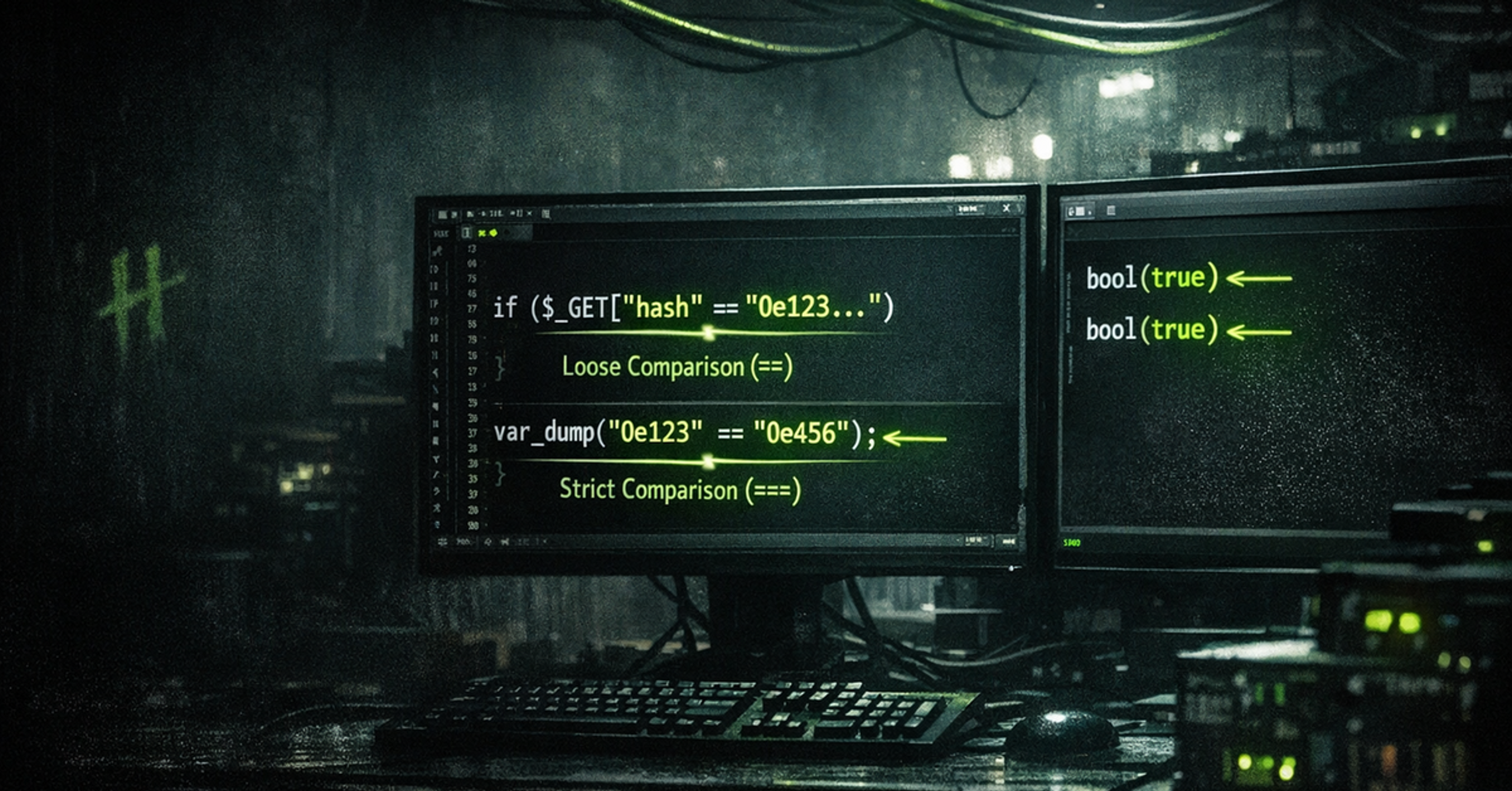
WEBType-juggling vulnerabilities
Automatic type conversion of a programming language can lead to unexpected results that can be exploited by an attacker
 WEB
WEBPDF export injection
PDF file generators are common and for good reason. However, dangerous vulnerabilities have been found in these in recent years.
 NETWORK
NETWORKWireshark
Wireshark is a tool used to capture and analyze data traffic. The tool is suitable for learning different network protocols and you often need it in CTF competitions as well.
 DEFENSE
DEFENSEBasics and concepts of information security monitoring
In this course, we go through the concepts related to the organization's information security control.
 CRYPTO
CRYPTOCryptography
From the history of cryptography to current use, the basics of encryption, technologies, applications and their impact on security.
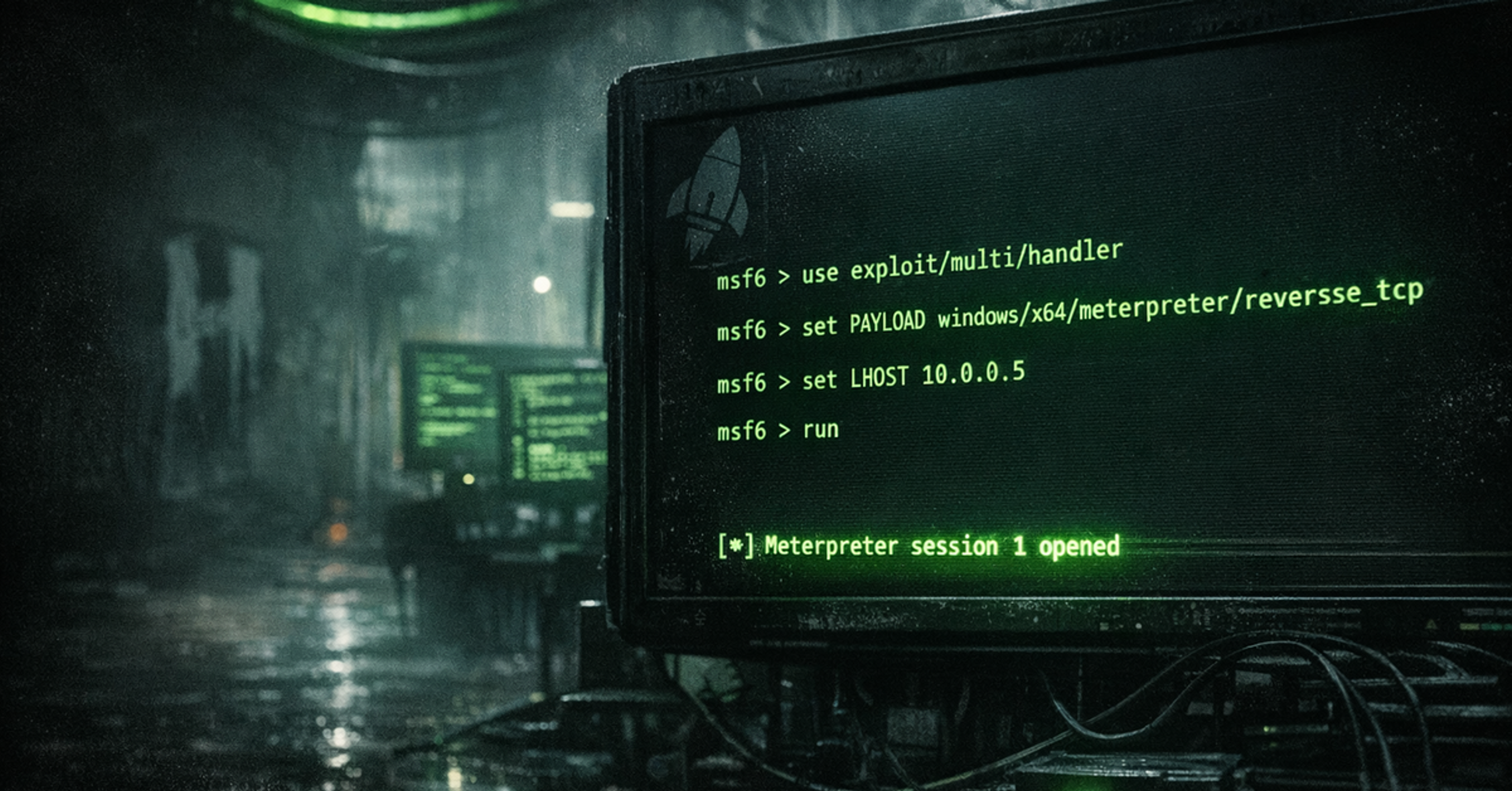 PWN
PWNMetasploit
Metasploit is a popular attack framework that helps professionals identify and exploit security holes. In this course, you will go through the use of Metasploit and learn how it can be used to carry out attacks and find security holes.
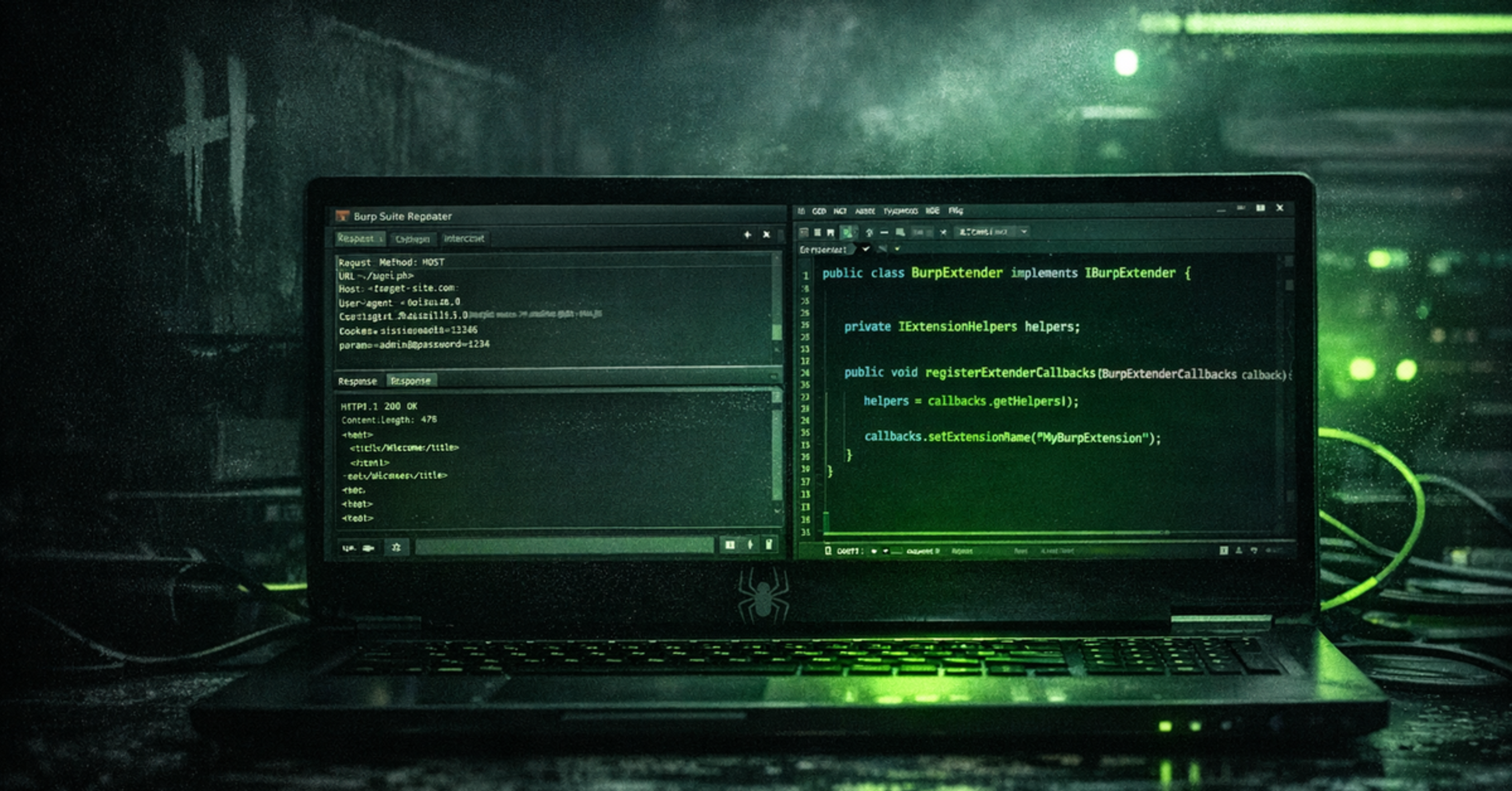 WEB
WEBBuilding BurpSuite Extensions
The course delves into advanced development with Burp Suite and teaches effective use of its extension API. We will build several practical extensions to address common challenges encountered during testing
 NETWORK
NETWORKComputer Networks
Let's get to know computer networks and network protocols in a little more depth than the basic course. A prerequisite for getting by, for example, with Nmap and Wireshark courses.
 DEFENSE
DEFENSENessus
Nessus is a widely used security assessment tool designed to identify vulnerabilities and weaknesses in computer systems, networks and applications.