Windows - Attack and Defense
Windows is everywhere
Windows is widely used in the IT environments of numerous companies and educational institutions, and Windows networks are typically managed through an Active Directory domain.
In this course, we will explore the security of the Windows operating system and Active Directory from the perspectives of both attackers and defenders. Some of the tasks involve attacks, while others are hardening tasks.
Windows is colossal!/Windows is huge!
The scope of the course (Windows, attack and defense) is quite broad. If one were to study it purely in theory, the course would be dull. On the other hand, without any theory, there would be no hacking because both attack and defense rely on understanding what is happening.
We chose, for these reasons, to implement the course using a scenario-based approach, where each section of the course deals with one "scenario" that may include a few attacks, a few tools, and a few hardenings to protect against the attacks.
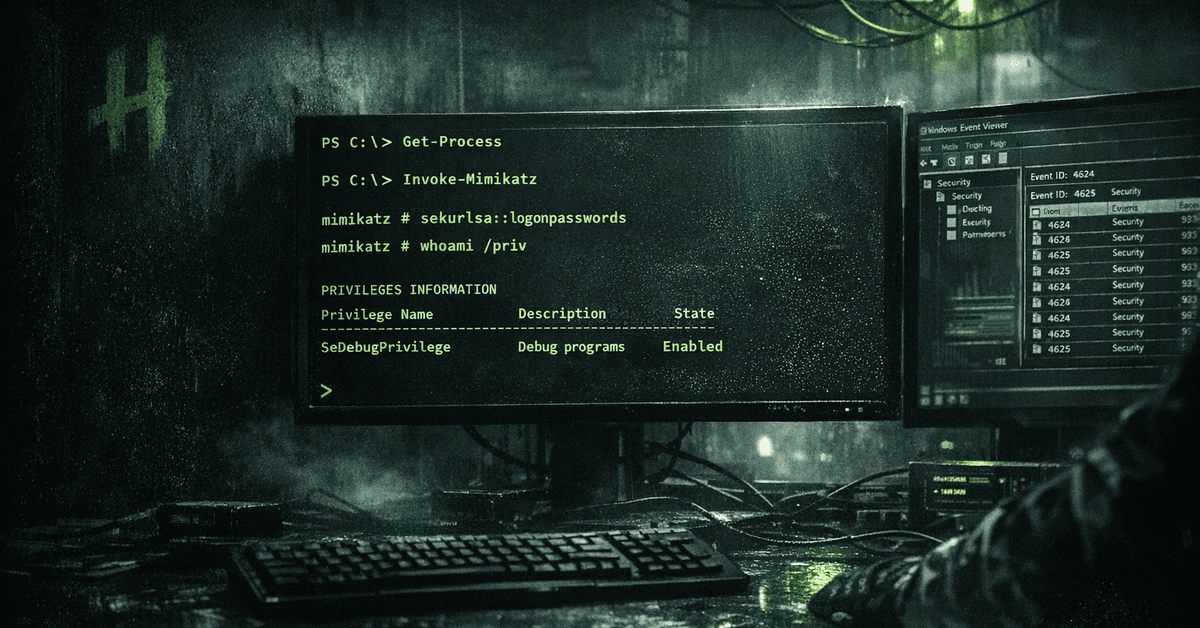
Let's truly understand things
The theory is covered in small pieces in practical context, always when necessary. Things are tried to be understood at the bit level in order to avoid the unfortunate phenomenon typical of such courses where the student knows how to try the psexec attack after obtaining the NTLM hash, but does not understand at all what the attack does and how it works (spoiler: psexec is based on the Service Control Manager RPC interface, which launches the desired command as a Windows service on the target server). Let's peek under the hood with Wireshark and dig into the source code of modules, for example, Metasploit.
This way, a comprehensive and theoretical topic will hopefully become fun and easily approachable step by step.
EvilCorp is waiting
Are you ready to break into EvilCorp's corporate network?

The course does not require knowledge of Windows environments, but otherwise basic things like Linux, computer networks, nmap, etc. would be good to have. Welcome to the course!
This course is still under construction, more scenarios will be added.
This course is in BETA mode, please let us know if you come across any misaligned bits.
Learn to hack — start here
Hundreds of interactive courses, virtual labs and CTF challenges in your browser. Start a free trial — no card required.