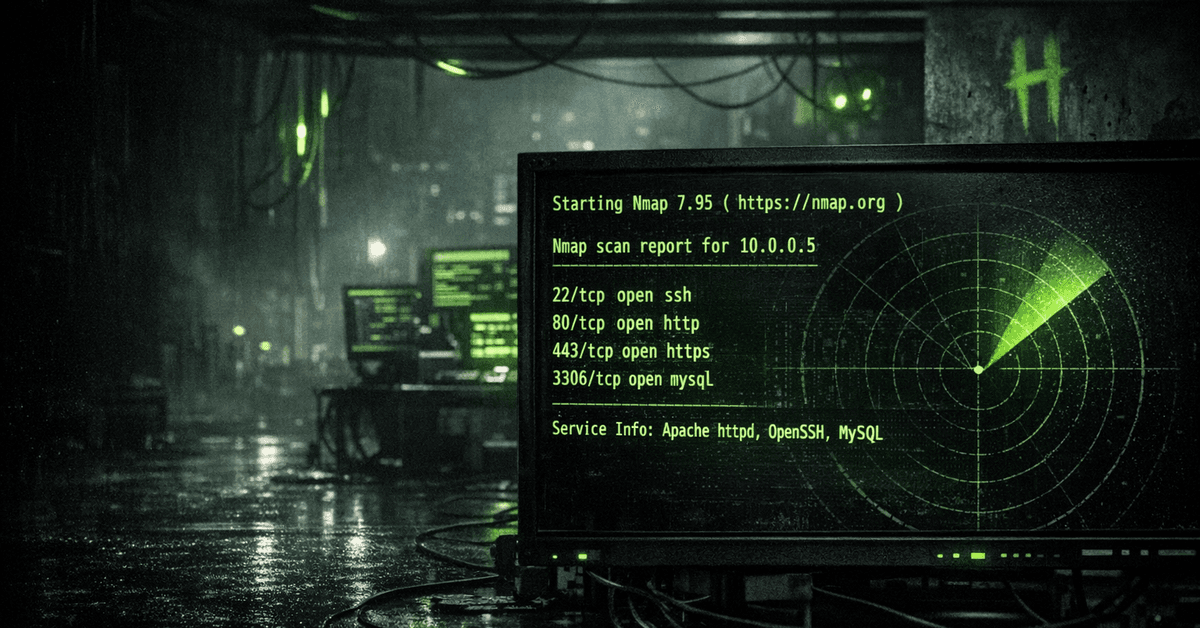
Nmap
Nmap is one of the most well-known network scanning tools, often used by cybersecurity experts. In this course, we will learn how to use this tool and explore its capabilities. Additionally, we will examine the traffic generated by the tool and analyze the pros and cons of different scanning methods. It is beneficial to have an understanding of how networks operate in this course.
Warning! - Conducting network scans without permission may cause system malfunctions and/or crashes. Please refrain from attempting to scan any address/system without certainty that said system is in your possession or that you have permission to do so.
Learn to hack — start here
Hundreds of interactive courses, virtual labs and CTF challenges in your browser. Start a free trial — no card required.