COURSE
Access control vulnerabilities
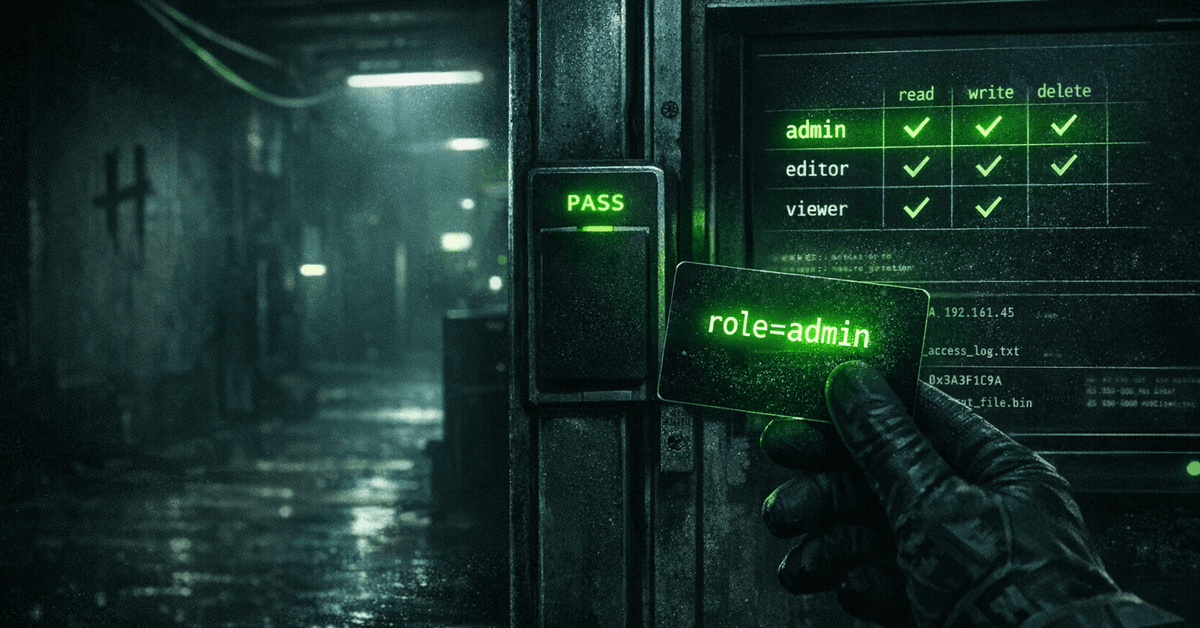
Development is evolving and thanks to modern application frameworks, traditional injection vulnerabilities or authentication problems are seen less and less frequently. However, one thing that always seems to remain equally difficult to implement securely is complex application access control.
DIFFICULTYBEGINNER
ESTIMATED TIME45min
Hakatemia Pro
Learn to hack — start here
Hundreds of interactive courses, virtual labs and CTF challenges in your browser. Start a free trial — no card required.